
Ways to ensure clean workstations
A tidy workstation can help employees become high achievers. Cleanliness also contributes to employee health, safety, and better office hardware maintenance. Is it time for
Ohio HB 96 / ORC 9.64 Has Gone Into Effect
Stay informed, stay secure, and stay ahead. Eaton Computer’s resource center gives you access to helpful insights, expert advice, and ongoing updates to support your business technology goals.

A tidy workstation can help employees become high achievers. Cleanliness also contributes to employee health, safety, and better office hardware maintenance. Is it time for
Remote work policies require companies to expand their communication capabilities. Many businesses aim to increase productivity and improve customer service by turning to a VoIP
When it comes to website analytics, traffic isn’t everything. Engagement with your site content is a better indicator that visitors to your website convert into

Microsoft Office is one of the most installed software suites in the world. If you are looking to integrate it into your company, you can

There are countless technology-related trends that come and go, but one of the most important technologies that business owners are sticking with is the cloud.

Running a business can be time-consuming, especially if you’re managing staff, looking for growth opportunities, and looking after clients. This leaves you little time to

Social media management for businesses can be boiled down to two simple sentences: The internet is full of trolls. Don’t feed the trolls. Read on

We’ve come to rely on our smartphones to help complete daily tasks, and this has resulted in the need to recharge our phones multiple times

Virtualization is the act of moving a physical component or bit of software from a physical environment to a digital one that’s normally delivered over

If you’re an iPhone user who’s always on the go, you may be texting sensitive information on a daily basis. One small mistake could have
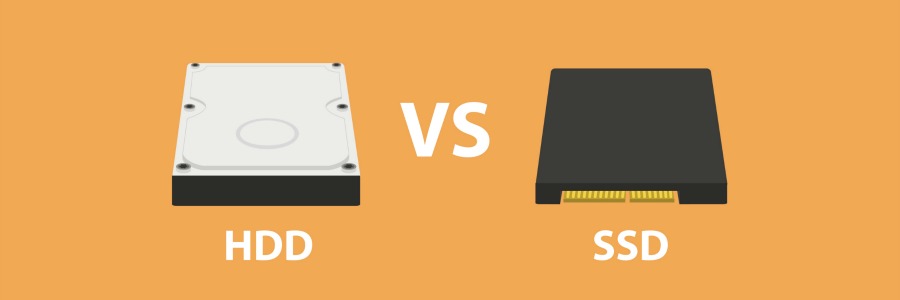
Buyers used to have a limited choice for what kind of storage they got with their laptop or desktop PCs. With the invention of the

When transitioning from traditional phone systems to Voice over Internet Protocol (VoIP) solutions, people often overlook the way calls are put on hold. However, doing